As the core foundation, the award winning real-time threat detection Guardian platform empowers clients by mechanising network defenses on a pro-active and real-time basis through:
Guardian
Through the unique combination of our people, technology and continuous innovation, we assist clients navigate the uncertain world of cyber risk. Our near real-time predictive analytics enable us to identify problems before they happen.
Insiox Guardian platform
- Providing clients with a single view across complex heterogeneous network architectures;
- Machine assisted predictive analytics to amplify your response capabilities through rapid and real-time responses to pre-indicators of an attack;
- Rapid development with zero integration risks, customisable to bespoke cyber needs with no integration risk to current infrastructures;
- Access to a team of trained cyber analysts actively threat hunting for new threats within the client business environment on a 24/7/365 basis; and
- Detailed remediation advice to expedite remediation efforts.
Continuous Vulnerability Assessment
Insiox utilises Nessus® to perform vulnerability scans and compliance audits. The goals/objectives of the vulnerability assessments are to provide management with a cyclical scanning and vulnerability assessment of the vulnerabilities on the in-scope environments in order to:
- Identify (vulnerability assessment) whether vulnerabilities exist on the critical IP addresses, provided by management, which could be exploited to gain access to the internal network, system and resources.
- Assess whether the network is actively being monitored to ensure administrator is notified in a timely manner of any security violations.
Managed Detection and Response
Our cyber security Threat Hunting Centre will actively hunt for threats within the client environment and will rapidly notify clients of potential threats or suspicious activity as well as the necessary remediation advice required to effectively respond and contain identified incidents.
Our offering includes:
- Passive monitoring of network communications for emerging cyber threats, sensitive data disclosure, and critical system vulnerabilities.
- Qualifying and quantifying cybersecurity risks through data-driven and risk-based remediation, this includes auto-alerting for both high and critical alerts.
- Through the Insiox Guardian platform, providing detailed insight into a customer network activity and allows for proactive incident response.
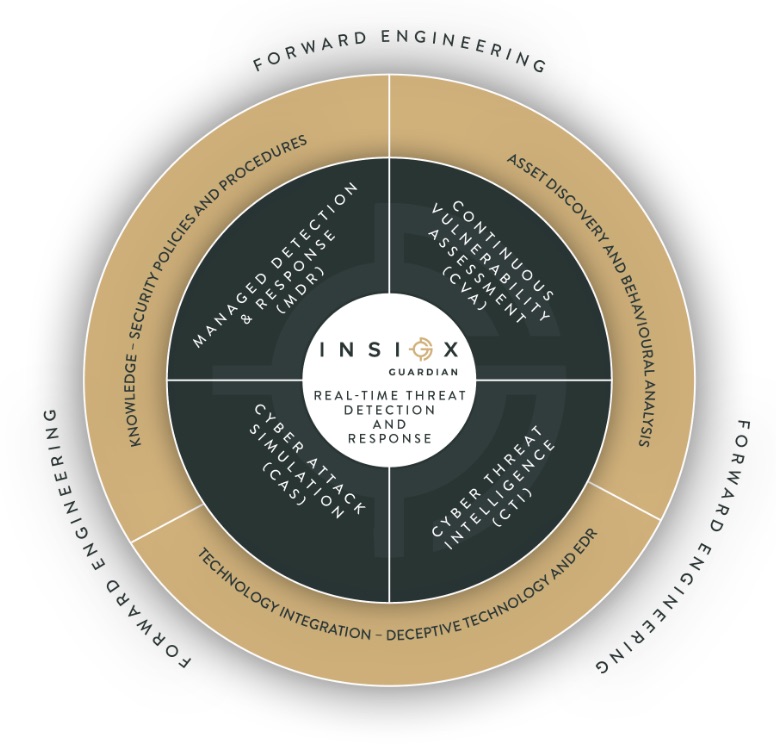
Cyber Threat Intelligence
By leveraging our real-time data fusion capability, we provide clients with emerging threat analysis which includes, but is not limited to:
- Cyber threat intelligence, monitoring, alerting, reporting and consulting.
- Global cybercrime, fraud, corporate espionage and attacker tradecraft analysis.
- Global cross-border, key and critical infrastructure being actively targeted.
- Offensive technology (e.g. malware) reverse engineering and countermeasures.
- Countermeasure, counterintelligence and counter-attack recommendations.
Continuous Attack Simulation
The unique Continuous Attack Simulation offering provides clients with a comprehensive approach to cyber assurance and continuous control testing of their digital defences.
This offering includes:
- Uninformed monthly security testing and environment assessments by skilled penetration testers
- Effectiveness testing of both detective and preventive controls
- Specifically, crafted awareness and cyber resilience campaigns
- Promoting shareholder confidence through independent assurance testing of the cyber control environment

